Resource Center
Welcome to our cybersecurity resource center where we uncover how malicious actors exploit weaknesses in systems, while going beyond the technical aspects and examining real-world perspectives across various industries.
Here you’ll find extensive research and insight from the well-known Horizon3.ai attack team, intuitive perspectives on everything security, and real-world attack path short stories that come directly from discoveries made by NodeZero.
Filters
Showing 1–6 of 412 results
Horizon3.ai Unveils Rapid Response Service for Cyber Resilience
Business Wire 03/25/2024 Horizon3.ai, a pioneer in autonomous security solutions, today announced the launch of its Rapid Response service, now part of the NodeZero™ platform. This one-of-a-kind capability marks a significant advancement in autonomous penetration testing solutions by addressing a critical gap in measuring the real-world impact of exploitable vulnerabilities within the software many organizations… Read the entire article here
Read More NodeZero: Testing for Exploitability of Palo Alto Networks CVE-2024-3400
On April 12 (and then updated again on April 20), Palo Alto Networks released an advisory about a vulnerability in the PAN-OS® software that runs Palo Alto Networks® Next-Generation Firewalls (NGFWs).
Read More Fortifying the Chain: A Proven Strategy for Supply Chain Defense
Understanding the Landscape of Cyber Threats and the Innovations in Supplier Security Posture Management
Read More Fireside Chat: Horizon3.ai and JTI Cybersecurity
Horizon3.ai Principal Security SME Stephen Gates and JTI Cybersecurity Principal Consultant Jon Isaacson discuss: - What JTI does to validate things like access control, data loss prevention, ransomware protection, and intrusion detection approaches. - How #pentesting and red team exercises allow orgs to validate the effectiveness of their security controls. - Why offensive operations work best to discover and mitigate...
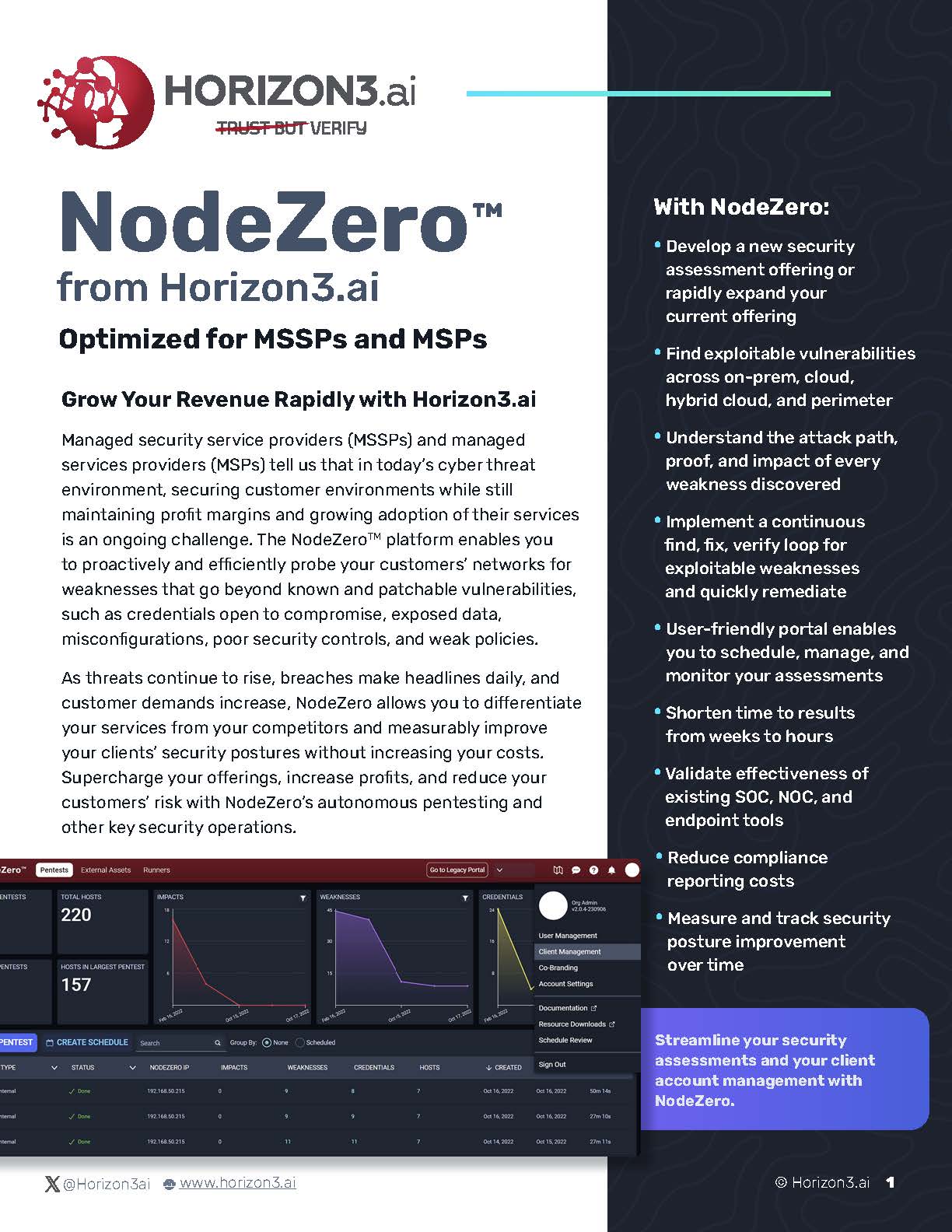
Read More NodeZero™ from Horizon3.ai Optimized for MSSPs and MSPs
The NodeZero platform enables you to proactively and efficiently probe your customers’ networks for weaknesses that go beyond known and patchable vulnerabilities, such as credentials open to compromise, exposed data, misconfigurations, poor security controls, and weak policies.
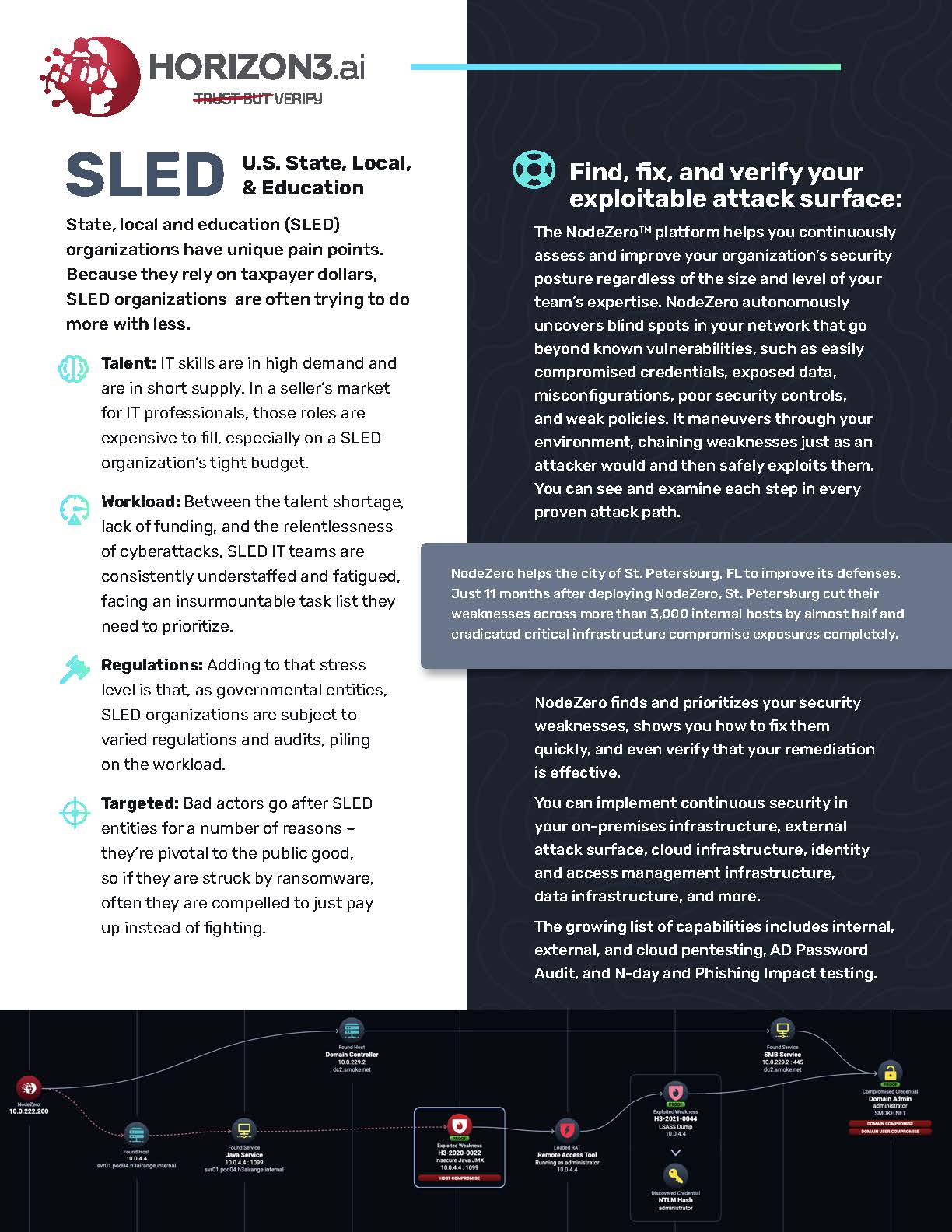
Read More SLED U.S. State, Local, & Education
State, local and education (SLED) organizations have unique pain points. Because they rely on taxpayer dollars, SLED organizations are often trying to do more with less.
Read More