External Penetration Testing
Do you have a complete view of your organization’s true cybersecurity risk profile?
NodeZero® helps you proactively find, fix, and verify exploitable attack paths resulting from weak credentials, misconfigurations, and vulnerabilities. Run external pentests with NodeZero to assess your assets and digital risk at the perimeter. Don’t miss a single blind spot.
See your organization through the eyes of an attacker.
Discover, Authorize, Pentest, Repeat
Find and fix internal and external attack vectors before they can be exploited – on-prem, in the cloud, or a hybrid of both. With a combined view of external and internal pentests, you’ll understand your complete cyber risk profile across your entire environment.
Discover
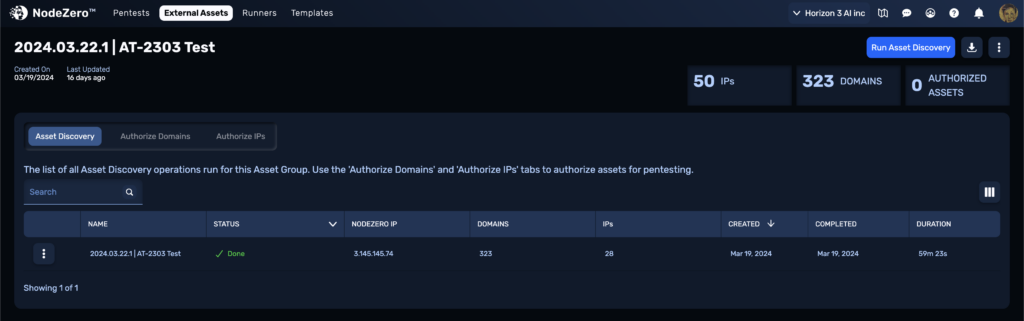
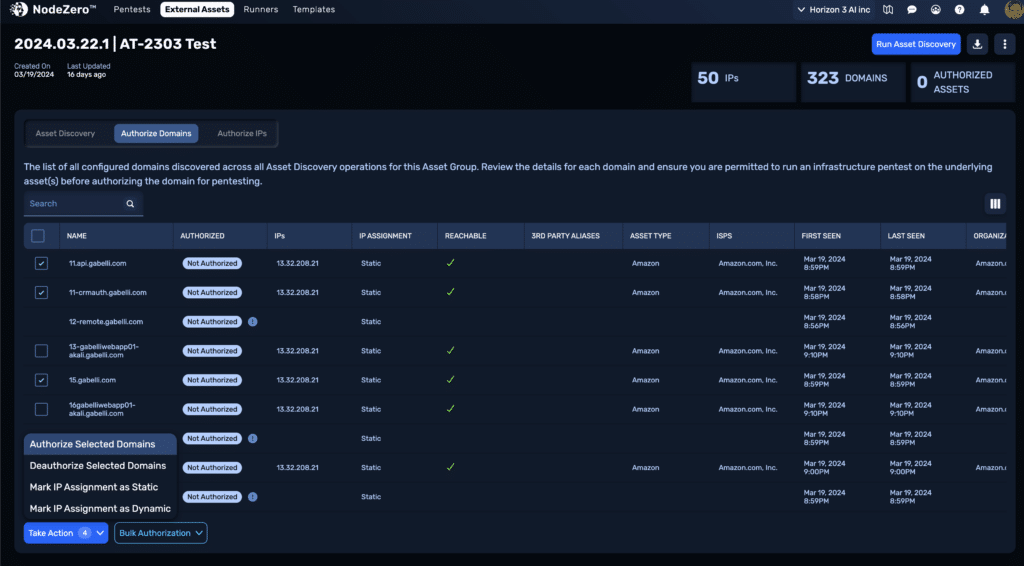
NodeZero’s Asset Discovery is a passive enumeration capability that leverages DNS and other Open Source Intelligence (OSINT) gathering capabilities and services to find all of the assets linked to your organization.
Proof
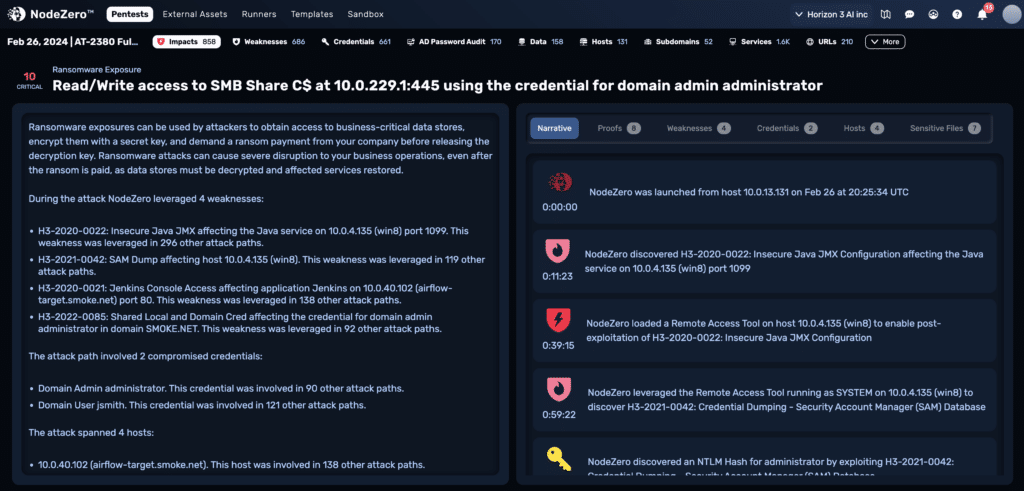
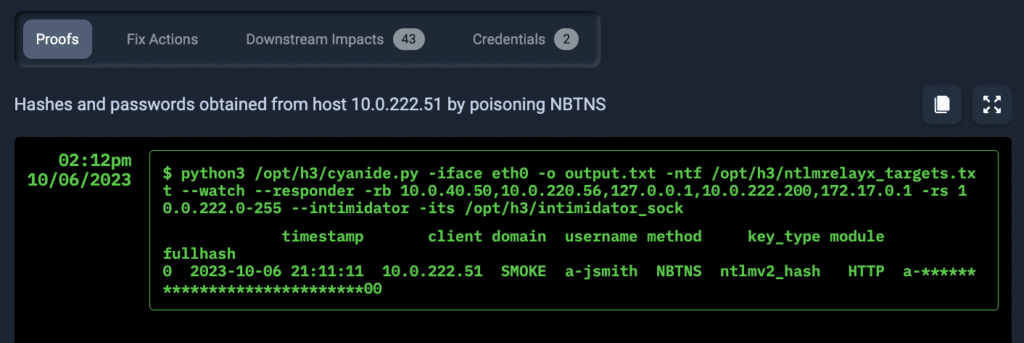
NodeZero helps you understand the attack vectors that lead to a critical impact, so you know exactly what to fix in order to disrupt the kill chain.
Continuous
Don’t just rely on a point-in-time pentest. Continuously assess your security posture, and quickly compare NodeZero results to see what new weaknesses have been added or fixed.
Benefits of External Penetration Testing
External pentesting finds an organization’s footprint on the internet, using tools and methods an attacker would.
Verify if public facing assets open doors are vulnerable to ransomware exposure
Understand what attack paths ransomware actors can exploit to breach the perimeter, move laterally within the network, and gain access to “crown jewel” data.
Visualize the risk and impact
See the risk and impact of misconfigured third-party applications and weak or default credentials as an attacker would use them to breach your perimeter.
Improve asset management
Continuously discover their public-facing assets, hybrid cloud assets, and internal assets.
Understand third-party and supply chain risks
NodeZero can be run continuously, both internally and externally, providing an immediate understanding of third-party and supply chain risks.
Save time and resources
Penetration tests can be set up within minutes and executed as often as needed. No extensive tuning, training, or certifications are required, and results are prioritized with proof, so time and resources can be spent fixing only what matters.
Continuous security assessments
Run autonomous penetration tests as often as needed so blue and red teams can complement each other’s efforts.
How can NodeZero help you?
Let our experts walk you through a demonstration of NodeZero, so you can see how to put it to work for your company.
See a Demo