NodeZero® for the Public Sector
See Your Environment the Way Attackers Do—Before They Do
The public sector remains one of the most targeted domains in cybersecurity. From overburdened city governments to mission-driven school systems, attackers are exploiting weak credentials, unpatched vulnerabilities, and misconfigured services to gain a foothold—and cause disruption.
State, Local, and Education (SLED) organizations are particularly vulnerable. Limited staff. Budget constraints. Expanding attack surfaces. And now, increasingly targeted attacks.
Meet NodeZero®: Offensive Security Built for SLED
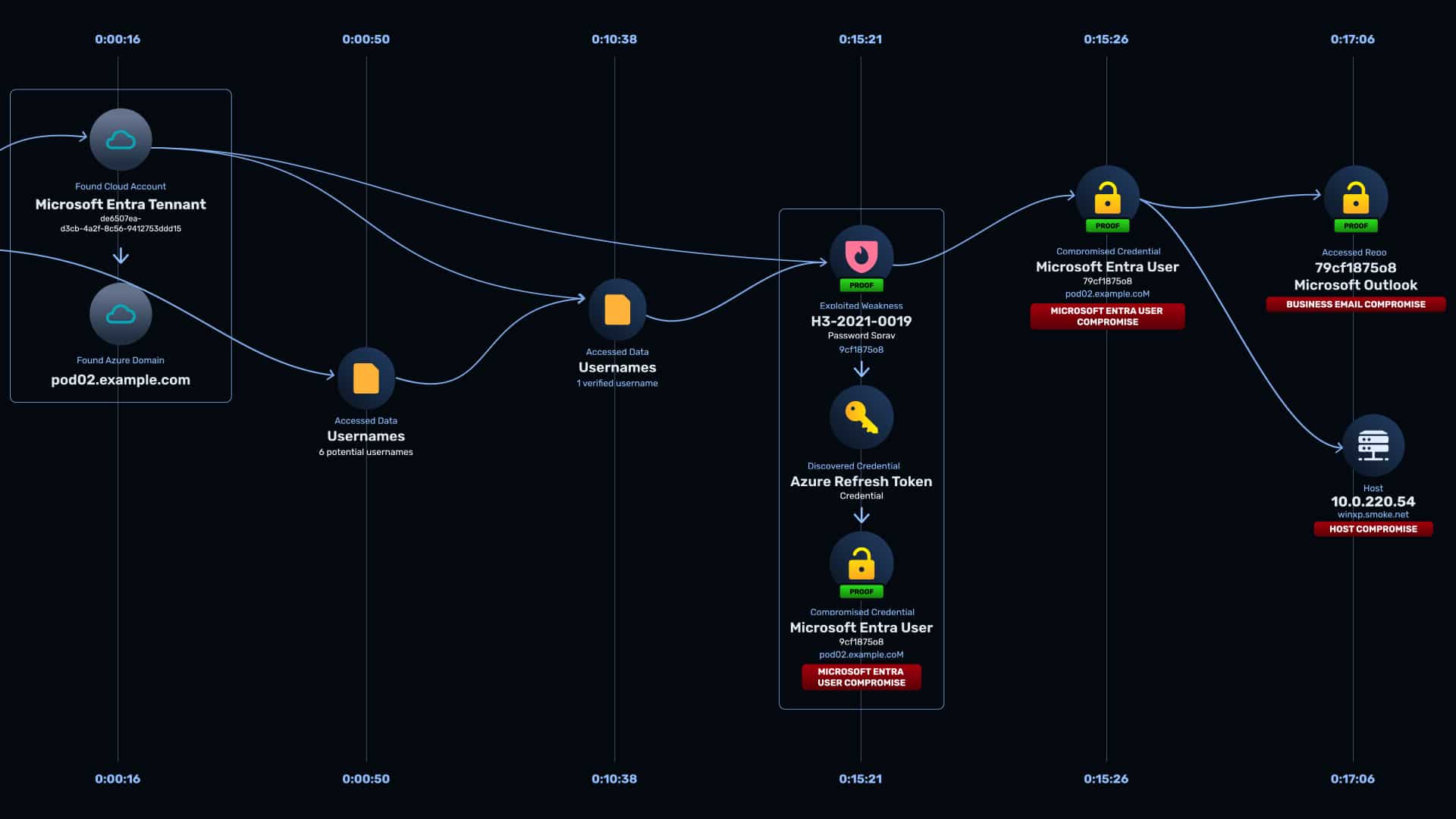
NodeZero isn’t a scanner. It’s not a simulation. It’s a fully autonomous pentesting platform that behaves like a real attacker—with one critical difference: it’s on your side.
- Launch pentests anytime—against real production systems
- Uncover and prove actual attack paths, not just theoretical risks
- Prioritize what matters with proof-based findings
- Retest fast to verify fixes and prove readiness
Whether you’re defending a state agency, a city network, securing a K-12 district, or maintaining uptime at a public university, NodeZero helps your team stay ahead of threats.
Designed for Small Teams, Big Missions
NodeZero empowers lean IT and security teams across the public sector. No agents. No appliances. No waiting. Just real results, fast.
- Autonomous operations: internal/external pentesting, AD audits, and more
- Support for on-prem, cloud, identity, and hybrid environments
- Safe for production—run tests during work hours with confidence
- Run unlimited tests across any scope, anytime
From Reactive to Ready
Most SLED organizations only find out they’re vulnerable after they’ve been exploited. NodeZero helps you get ahead of the threat curve by continuously verifying where you’re vulnerable—and showing how attackers could exploit it.
That’s not just cybersecurity. That’s proof-based readiness.
Real Impact
Organizations like the City of St. Petersburg, Moravian University, and Regina International Airport are using NodeZero to uncover hidden vulnerabilities, validate remediations, and stay resilient in the face of rising threats. And they’re doing it without hiring more headcount or adding new defensive technologies.