Security you can prove.
Get continuous clarity into your threat risk and exposure.
Fight AI with AI. Continuously and safely hack your production environment, fix what matters most, verify instantly, and repeat autonomously.
5,200
customers
Trusted by NSA and 4 of the Fortune 10
You’ve invested millions. Can you prove you’re secure?
AI has shifted the advantage to the attacker. While your team drowns in noise and manual patches, AI has handed attackers unprecedented scale and speed.
Stop guessing. Start proving.
Move from vulnerability management to closing proven attack paths in just a few clicks.
Hack
Prove exploitability with real attacks.
Knowing a vulnerability exists isn’t enough. You need to know if it’s actually exploitable.
Fix
Prioritize what actually matters.
In an ocean of vulnerabilities, prioritize the ones that are proven to endanger your business.
Verify
Close the loop on every fix.
Don’t just check a box. Re-test to confirm the threat is gone and prove your risk has actually been reduced.
Repeat
Prove continuous resilience.
Your risk changes every time your environment does. Continuously find weaknesses before attackers do — so you stay secure through every change, every day.
Hack
Prove exploitability with real attacks.
Knowing a vulnerability exists isn’t enough. You need to know if it’s actually exploitable.
Fix
Prioritize what actually matters.
Not every vulnerability is worth your time. Prioritize the ones that protect your business.
Verify
Close the loop on every fix.
Don’t just check a box. Re-test to confirm the threat is gone and prove your risk has actually been reduced.
Repeat
Prove continuous resilience.
Your risk changes every time your environment does. Continuously find weaknesses before attackers do — so you stay secure through every change, every day.
Real AI-driven attacks, run safely in production.
Horizon3.ai’s NodeZero® autonomously executes real attack techniques, without agents or disruption. We proactively show exactly how attackers move, what they access, how to stop them, and verify fixes instantly.
Proactively prove that you're resilient.
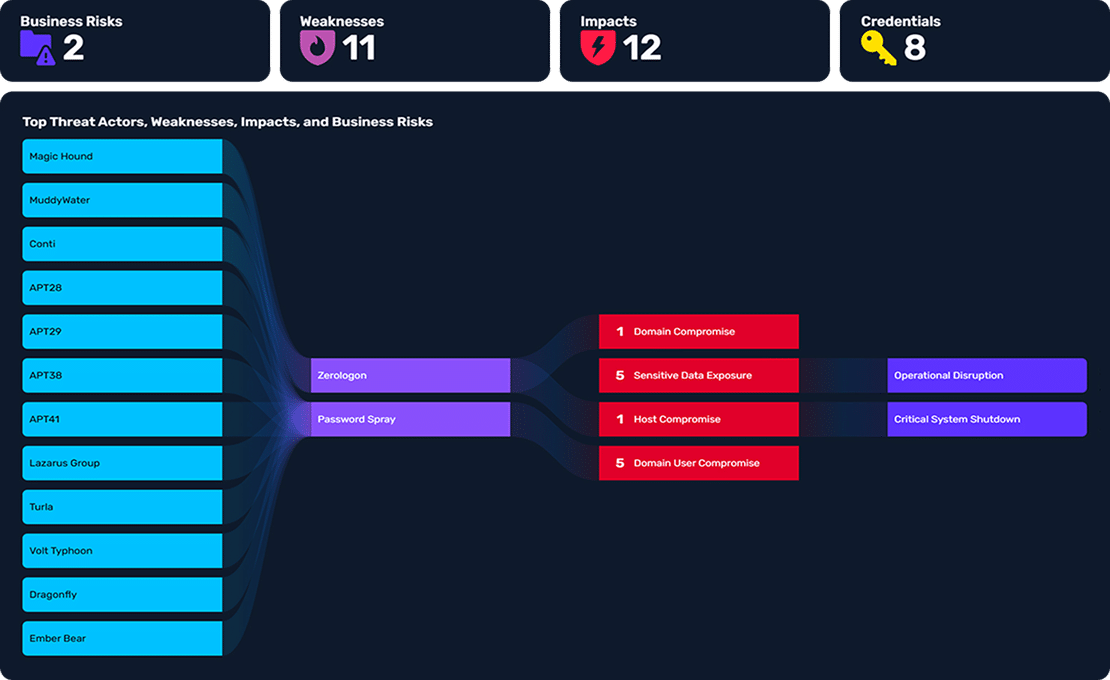
NodeZero isn’t a scanner. We show you the real risk and impact on your business.
Know exactly where you stand so you can stop guessing and start proving your security posture with confidence.
Why trust Horizon3.ai
We put the World’s Best AI Hacker™, NodeZero️, on your side to safely run in production — because production is where the hackers attack.
Purpose-built AI
NodeZero uses the right AI for the right problem, from machine learning to GenAI. We deliver repeatable, evidence-based results with zero hallucinations.
Learns at machine scale
NodeZero learns from hundreds of thousands of autonomous tests in production — outpacing the collective history of manual pentesting in just one year.
Proven production-safe
NodeZero has achieved zero downtime across all production tests, earning the trust of the world’s most sensitive high-security environments.
Evidence, not opinion.
Don’t just take our word for it.
225,000
pentests safely run in production
Horizon3.ai is trusted by global governments, Fortune 10 giants, and major healthcare providers, where the need for security and safety is absolute.
“…without taking an attacker’s perspective by considering actual attack vectors that they can use to get in, you really can’t be ready.”
Jon Isaacson
Principal Consultant
#1 in Security
Inc. 5000 Fastest Growing Companies

#3 overall
Deloitte Technology Fast 500
#4 in Security
Fast Company’s Most Innovative Companies