It took just two days for a pair of researchers from Horizon3.ai to discover exploits for the new F5 BIG-IP vulnerability, and have called for devices to be immediately updated to protect against bad actors. The vulnerability, they said, is trivial to exploit and expect adversaries to begin creating exploits soon.
“F5 disclosed a security issue Wednesday with their popular BIG-IP products,” says Zach Hanley, Chief Attack Engineer at Horizon3.ai. “Then James (Horseman, Exploit Developer with Horizon3.ai) and I were trying to figure out what the issue was to weaponize it.”The flaw, found in the iControl REST authentication component, could allow attackers to bypass an authentication check, enabling elevate privileges, inject ransomware, steal data, or enact a system takeover.
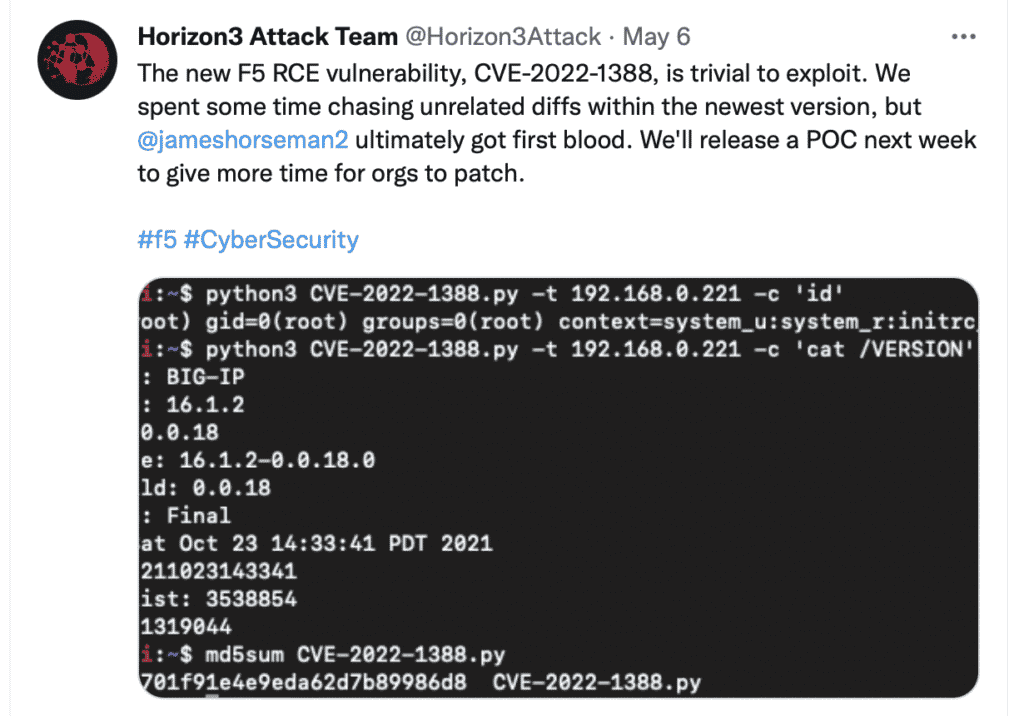
Horizon3.ai has publicly released their POC exploit to push organizations to patch their devices.
“The hope is to push organizations to patch given its simplicity,” says Hanley.
Last Friday the team passed their POC to GreyNoise to build early detections. More information can be found here: CVE-2022-1388.
Industry publications immediately covered the discovery, including Bleeping Computer, Computing, and Security Week.
Follow the Horizon3.ai Attack Team (@Horizon3Attack) on Twitter for updates on this issue and more. For a technical deep dive into this topic, you can check out the Attack Team’s own blog entry where they go into full details about their research.




